Tyler Cohen Wood
- Former U.S. Department of Defense Senior Intelligence Officer
- Named ‘Top 30 Women in AI’ and ‘Cyber Woman of the Year’ Finalist
- Delivers practical insights on AI and technology’s impact on business, security, and society

Tyler Cohen Wood Speaker Biography
Tyler Cohen Wood is an internationally recognized technology strategist, keynote speaker, and thought leader with over two decades of experience at the intersection of national security, innovation, and emerging technologies. As a former U.S. Department of Defense Senior Intelligence Officer and Deputy Division Chief at the Defense Intelligence Agency (DIA), Tyler has advised the White House, military leaders, and federal agencies on complex tech threats and future-focused digital strategy. She has also worked in the private sector as a Director of Cyber Risk Management at AT&T, and previously held roles with General Dynamics, IBM, and NASA, using her expertise to protect intellectual property and global customers from hackers.
As the Founder & CEO of Guardian Petal, the first AI-powered protective harness line for dogs, Tyler is pioneering a revolutionary blend of fashion, safety, and intelligent technology. She is also the host of the Our Connected Life podcast and a sought-after voice on the impact of Cybersecurity, AI and emerging tech.
Named one of the Top 10 Cybersecurity Keynote Speakers and a Top 30 Woman in AI, Tyler is also a proud member of Marquis Who’s Who. She has delivered electrifying keynotes at RSA, DefCon/Black Hat, Bloomberg, EY, FedEx, Raymond James, the Chicago Mercantile Exchange, TransUnion, Humana, Allstate, and Wells Fargo, empowering audiences to harness innovation, embrace disruption, and lead with confidence into the future.
Book this SpeakerFeatured Videos
Speech Topics
The Intelligence Era: What Everyone Needs to Know About AI & Emerging Tech
We’ve officially entered the Intelligence Era, where AI and emerging technologies are changing how we work, compete, and grow. Understanding these tools is no longer optional for professionals at any level – it’s mission critical.
In this keynote, Tyler Cohen Wood decodes how AI and emerging tech are impacting industries in real, practical ways. Drawing from her experience as a former U.S. intelligence leader and tech CEO, Tyler shares clear insights, current trends, and useful strategies that help audiences move from overwhelmed to empowered.
Whether your organization is just beginning to explore AI or already embracing it, this session will help you:
– Understand what AI means for your role and your industry
– Explore real-world use cases and opportunities
– Build confidence in using tech to drive growth and stay competitive
This is your guide to making smarter decisions, faster, in a rapidly evolving digital world.
The Intersection of Cybersecurity, Emerging Tech, and AI: Unmasking Deepfakes and Social Engineering
The convergence of cybersecurity, AI, and emerging technologies is reshaping the digital landscape and raising new threats. This eye-opening session explores the rise of deepfakes and the next generation of AI-powered social engineering attacks, revealing how these technologies are being used to blur reality and exploit human trust.
Experience a live deepfake demo that highlights just how convincing and dangerous these AI-generated forgeries can be. Learn how to detect them using practical tools and telltale signs. Explore how AI is being used to craft hyper-personalized phishing emails and voice simulations that target individuals and organizations with alarming precision.
This keynote delivers a compelling look at the urgency for stronger cybersecurity strategies, ethical safeguards, and proactive defense. You’ll leave informed, alert, and better equipped to navigate the risks at the intersection of AI and cyber deception.
Power Moves: Building Confidence and Momentum as a Woman in Today’s World
In fast-moving industries like tech and beyond, women are stepping into leadership roles with greater impact than ever. In this empowering keynote, cybersecurity expert and tech leader Tyler Cohen Wood shares her personal journey and the mindset shifts that helped her succeed in male-dominated environments.
Through engaging stories and practical insights, Tyler offers a roadmap for women to overcome challenges, build confidence, and grow into powerful leaders regardless of the industry they’re in. Attendees will walk away with actionable tools to strengthen their voice, take bold steps forward, and create meaningful impact in their careers.
Reviews
Tyler did a wonderful job sharing her dark web knowledge with our organization. Although the dark web is scary, Tyler made it easy to understand and clear how to secure your information.
Tyler is passionate and enthusiastic about her work. Lot of real time examples were covered by her, and very practical tips on how to improve our safety. Very good illustration of how all info connected together can endanger people close to us. Her Story telling skills were appreciated by all the participants. She was whole heartedly involved during the exchange of question and answers at the end of the session.
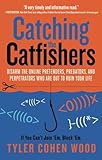
Books